Computers and Technology, 16.01.2020 00:31 juicemankinnie95
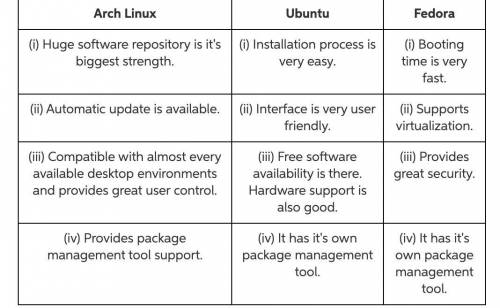
Research three different distributions of linux on the internet. record where you went to obtain your information. compare and contrast the different distributions with regard to their strengths and the packages available for each. after you finish, locate and visit two linux newsgroups. how did you locate them and where did you obtain the information? what are the topics specific to each? find two questions per newsgroup posted by a user in need of a solution to a problem, and follow the thread of responses suggested by others to solve that problem.

Answers: 3


Another question on Computers and Technology

Computers and Technology, 22.06.2019 08:10
Alook-up table used to convert pixel values to output values on a monitor. essentially, all pixels with a value of 190 or above are shown as white (i.e. 255), and all values with a value of 63 or less are shown as black (i.e. 0). in between the pixels are scaled so that a pixel with a value p is converted to a pixel of value 2/127 −+3969). if a pixel has a value of 170 originally, what value will be used to display the pixel on the monitor? if a value of 110 is used to display the pixel on the monitor, what was the original value of the pixel?
Answers: 1

Computers and Technology, 22.06.2019 12:50
You have just been hired as an information security engineer for a large, multi-international corporation. unfortunately, your company has suffered multiple security breaches that have threatened customers' trust in the fact that their confidential data and financial assets are private and secured. credit-card information was compromised by an attack that infiltrated the network through a vulnerable wireless connection within the organization. the other breach was an inside job where personal data was stolen because of weak access-control policies within the organization that allowed an unauthorized individual access to valuable data. your job is to develop a risk-management policy that addresses the two security breaches and how to mitigate these risks.requirementswrite a brief description of the case study. it requires two to three pages, based upon the apa style of writing. use transition words; a thesis statement; an introduction, body, and conclusion; and a reference page with at least two references. use a double-spaced, arial font, size 12.
Answers: 1

Computers and Technology, 22.06.2019 19:30
The following is an excerpt from a slide presentation. today we will inverse operations solving equations using inverse operations solving inequalities using inverse operations from which part of the presentation does the slide most likely come from? a. introduction b. outline c. body d. conclusion
Answers: 1

Computers and Technology, 22.06.2019 20:00
How is the number 372 written when expanded out to place values in the base 8 (octal) number system? a. 2 x 4 + 3 x 2 + 4 x 1 b. 3 x 64 + 7 x 8 + 2 x 1 c. 3 x 8 + 7 x 7 + 2 x 6 d. 3 x 100 + 7 x 10 + 2 x 1
Answers: 1
You know the right answer?
Research three different distributions of linux on the internet. record where you went to obtain you...
Questions

English, 30.08.2020 01:01


Mathematics, 30.08.2020 01:01

Chemistry, 30.08.2020 01:01

Health, 30.08.2020 01:01


Mathematics, 30.08.2020 01:01

Social Studies, 30.08.2020 01:01

Health, 30.08.2020 01:01

Mathematics, 30.08.2020 01:01

Computers and Technology, 30.08.2020 01:01

Biology, 30.08.2020 01:01





History, 30.08.2020 01:01

Arts, 30.08.2020 01:01

Mathematics, 30.08.2020 01:01

Chemistry, 30.08.2020 01:01