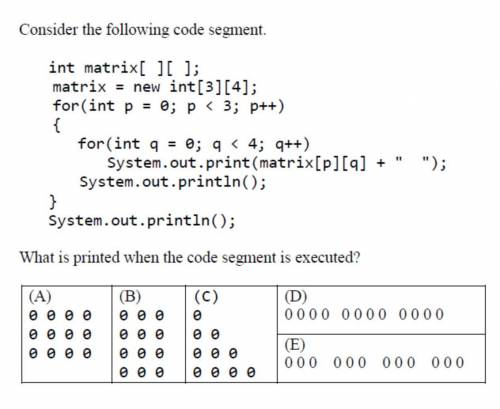
Consider the following code segment - 5
...

Computers and Technology, 02.03.2021 01:00 orlandoreypot2491
Consider the following code segment - 5

Answers: 3


Another question on Computers and Technology

Computers and Technology, 21.06.2019 22:30
Provide an example of a project that combines the three principles of lean six sigma with business project management (bpm) and services oriented architecture (soa). identify the elements of the project that comply with each of three principles.
Answers: 1

Computers and Technology, 22.06.2019 12:50
You have just been hired as an information security engineer for a large, multi-international corporation. unfortunately, your company has suffered multiple security breaches that have threatened customers' trust in the fact that their confidential data and financial assets are private and secured. credit-card information was compromised by an attack that infiltrated the network through a vulnerable wireless connection within the organization. the other breach was an inside job where personal data was stolen because of weak access-control policies within the organization that allowed an unauthorized individual access to valuable data. your job is to develop a risk-management policy that addresses the two security breaches and how to mitigate these risks.requirementswrite a brief description of the case study. it requires two to three pages, based upon the apa style of writing. use transition words; a thesis statement; an introduction, body, and conclusion; and a reference page with at least two references. use a double-spaced, arial font, size 12.
Answers: 1

Computers and Technology, 23.06.2019 13:30
What is the primary difference between the header section of a document and the body? a. the body is displayed on the webpage and the header is not. b. the header is displayed on the webpage and the body is not. c. the tag for the body is self-closing, but the tags for the headers must be closed. d. the tag for the header is self closing, but the tag for the body must be closed.
Answers: 3

Computers and Technology, 23.06.2019 22:30
Apart from confidential information, what other information does nda to outline? ndas not only outline confidential information, but they also enable you to outline .
Answers: 1
You know the right answer?
Questions


English, 06.05.2021 01:00





English, 06.05.2021 01:00

Arts, 06.05.2021 01:00


Advanced Placement (AP), 06.05.2021 01:00

Mathematics, 06.05.2021 01:00


Mathematics, 06.05.2021 01:00

Mathematics, 06.05.2021 01:00



English, 06.05.2021 01:00

Mathematics, 06.05.2021 01:00

Mathematics, 06.05.2021 01:00

Mathematics, 06.05.2021 01:00



