Computers and Technology, 05.07.2021 19:20 tiatia032502
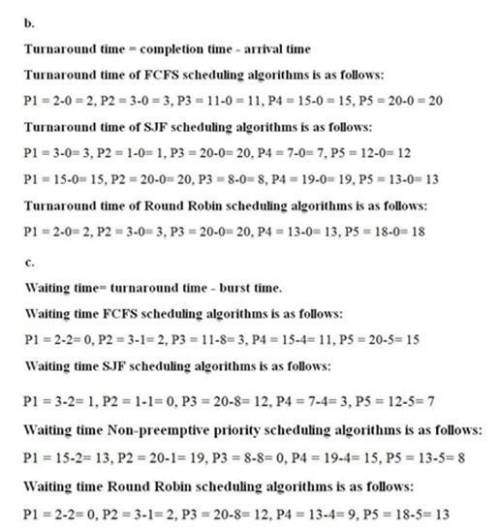
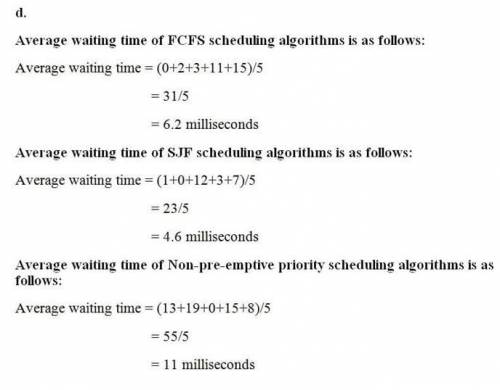
Consider the following set of processes, with the length of the CPU burst given in milliseconds:Process Brsut Time PrirorityP1 2 2P2 1 1P3 8 4P4 4 2P5 5 3The processes are assumed to have arrived in the order P1, P2, P3, P4, P5, all at time 0.Required:a. Draw four Gantt charts that illustrate the execution of these processes using the following scheduling algorithms: FCFS, SJF, nonpreemptive priority (a larger priority number implies a higher priority), and RR (quantum = 2).b. What is the turnaround time of each process for each of the scheduling algorithms in part a?c. What is the waiting time of each process for each of these scheduling algorithms?d. Which of the algorithms results in the minimum average waiting time (over all processes)?

Answers: 2


Another question on Computers and Technology

Computers and Technology, 21.06.2019 22:00
Your task this week is to write a very simple spam classifier in python. it will classify messages as either spam (unwanted) or ham (wanted). the program will have a set of spam_words, words that are known to appear in spam messages. that set is included in the template file spam.pypreview the document. you will also define a spam threshold which reflects the allowed percentage of spam words in the message. you'll compute a 'spam indicator', which is the ratio of spam words to the total number of unique words in the message. if the spam indicator exceeds the spam threshold, the message is classified as spam. otherwise it is classified as ham. we'll assume that the spam threshold is a constant and has a value of 0.10. your program will prompt the user for a message and then will print the corresponding spam indicator with two decimal digits and the corresponding classification (spam or ham). the program will be case insensitive. the spam words are detected whether they are in lower case or upper case or mixed case. each word, spam or not, is counted once (even if it appears multiple times in the message.) the program will remove punctuation from the message before identifying the words and computing the spam indicator. for example '! ' must be identified as the spam word 'now'.
Answers: 3

Computers and Technology, 23.06.2019 22:30
You draw two cards from a standard deck of 52 cards, but before you draw the second card, you put the first one back and reshuffle the deck. (a) are the outcomes on the two cards independent? why?
Answers: 3

Computers and Technology, 23.06.2019 23:40
Which of the following calculates the total from the adjacent cell through the first nonnumeric cell by default, using the sum function in its formula? -average -autosum -counta -max
Answers: 1

Computers and Technology, 24.06.2019 12:40
Match the feature to the network architecture. expensive to set up useful for a small organization easy to track files has a central server inexpensive to set up difficult to track files useful for a large organization does not have a central server client- server network peer-to-peer network
Answers: 3
You know the right answer?
Consider the following set of processes, with the length of the CPU burst given in milliseconds:Proc...
Questions



Mathematics, 07.10.2020 15:01

Mathematics, 07.10.2020 15:01

Biology, 07.10.2020 15:01


Business, 07.10.2020 15:01

History, 07.10.2020 15:01

History, 07.10.2020 15:01




Biology, 07.10.2020 16:01


Mathematics, 07.10.2020 16:01


Mathematics, 07.10.2020 16:01