
Computers and Technology, 05.10.2021 01:00 jangk
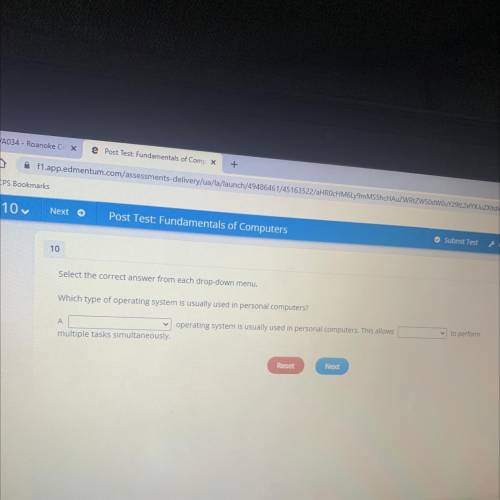
Select the correct answer from each drop-down menu.
Which type of operating system is usually used in personal computers?
to perform
А
operating system is usually used in personal computers. This allows
multiple tasks simultaneously.

Answers: 1


Another question on Computers and Technology

Computers and Technology, 22.06.2019 00:00
11. is the ability to understand how another person is feeling. a. authority b. sympathy c. empathy d. taking a stand
Answers: 1

Computers and Technology, 22.06.2019 00:40
Reading characters and strings from the keyboard: consider the following c++ program 1. #include 2. #include 3. using namespace std; 4. mystring1 5. 6. int main() 7. { 8. 9. string mystring1, mystring2; mychar1 10. 11. 12. char mychar1, mychar2; 13. 14. cout< < "enter a string: "; mychar2 15. 16. cin> > mystring1; // 17. cin.get(mychar1); 18. cin> > mychar2; 19. getline(cin,mystring2); mystring2 20. 21. 22. cout<
Answers: 1

Computers and Technology, 22.06.2019 10:00
Create a word problem that involves calculating the volume and surface area of a three-dimensional object. cube: surface area 6 s2 , volume s3
Answers: 3

Computers and Technology, 22.06.2019 12:50
You have just been hired as an information security engineer for a large, multi-international corporation. unfortunately, your company has suffered multiple security breaches that have threatened customers' trust in the fact that their confidential data and financial assets are private and secured. credit-card information was compromised by an attack that infiltrated the network through a vulnerable wireless connection within the organization. the other breach was an inside job where personal data was stolen because of weak access-control policies within the organization that allowed an unauthorized individual access to valuable data. your job is to develop a risk-management policy that addresses the two security breaches and how to mitigate these risks.requirementswrite a brief description of the case study. it requires two to three pages, based upon the apa style of writing. use transition words; a thesis statement; an introduction, body, and conclusion; and a reference page with at least two references. use a double-spaced, arial font, size 12.
Answers: 1
You know the right answer?
Select the correct answer from each drop-down menu.
Which type of operating system is usually used...
Questions

Social Studies, 06.03.2021 04:20

SAT, 06.03.2021 04:20




History, 06.03.2021 04:20




Mathematics, 06.03.2021 04:20


History, 06.03.2021 04:20

Mathematics, 06.03.2021 04:20

Computers and Technology, 06.03.2021 04:20



Chemistry, 06.03.2021 04:20

Mathematics, 06.03.2021 04:20




