Pls help its important
...

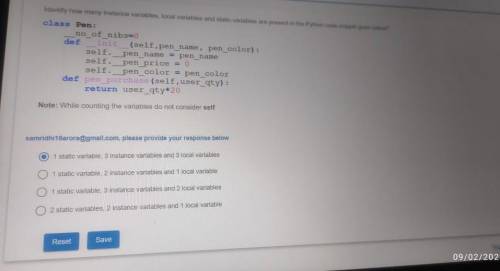
Answers: 1


Another question on Computers and Technology

Computers and Technology, 22.06.2019 03:50
You are working as a security analyst in a company xyz that owns the whole subnet range of 23.0.0.0/8 and 192.168.0.0/8. while monitoring the data, you find a high number of outbound connections. you see that ip's owned by xyz (internal) and private ip's are communicating to a single public ip. therefore, the internal ip's are sending data to the public ip. after further analysis, you find out that this public ip is a blacklisted ip, and the internal communicating devices are compromised. what kind of attack does the above scenario depict?
Answers: 3

Computers and Technology, 22.06.2019 15:30
When creating a budget, log fixed expenses before income. after income. after savings. at the top.
Answers: 1

Computers and Technology, 23.06.2019 11:30
Me dangers of social media and the internetexplain what each means: 1) social media and phones have become an addiction.2) outside people have access to you all the time.3) cyberstalking4) cyberbullying5) catphishing6) viruses7) identity theft8) credit card fraud9) hacking10) money schemes
Answers: 1

Computers and Technology, 23.06.2019 20:00
Me ajude por favor , coloquei uma senha e não consigo tira-la no chorme
Answers: 2
You know the right answer?
Questions

Mathematics, 22.05.2020 23:00

Mathematics, 22.05.2020 23:00



Mathematics, 22.05.2020 23:00



History, 22.05.2020 23:00



Mathematics, 22.05.2020 23:01






Mathematics, 22.05.2020 23:01

Mathematics, 22.05.2020 23:01