Mathematics, 20.09.2019 16:10 hannahbannana98
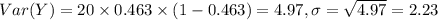
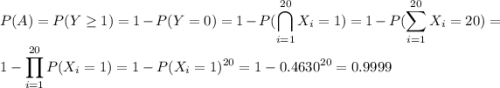
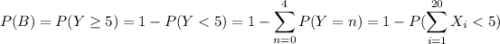
An article in information security technical report ["malicious software—past, present and future" (2004, vol. 9, pp. 6–18)] provided the following data on the top ten malicious software instances for 2002. the clear leader in the number of registered incidences for the year 2002 was the internet worm "klez," and it is still one of the most widespread threats. this virus was first detected on 26 october 2001, and it has held the top spot among malicious software for the longest period in the history of virology. place name % instances 1 i-worm. klez 46.30% 2 i-worm. lentin 17.83% 3 i-worm. tanatos 5.21% 4 i-worm. badtransii 1.30% 5 macro. word97.thus 1.80% 6 i-worm. hybris 0.11% 7 i-worm. bridex 0.35% 8 i-worm. magistr 0.02% 9 win95.cih 0.24% 10 i-worm. sircam 26.84% suppose that 20 malicious software instances are reported. assume that the malicious sources can be assumed to be independent. (a) what is the probability that at least one instance is "klez"? round your answer to four decimal places (e. g. 98.7654). (b) what is the probability that five or more instances are "klez"? round your answer to four decimal places (e. g. 98.7654). (c) what is the mean of the number of "klez" instances among the 20 reported? round your answer to two decimal places (e. g. 98.76). (d) what is the standard deviation of the number of "klez" instances among the 20 reported? round your answer to two decimal places (e. g. 98.76).

Answers: 3


Another question on Mathematics

Mathematics, 21.06.2019 16:20
Giuseppi's pizza had orders for $931.00 of pizzas. the prices were $21 for a large pizza, 514 for a medium pizza, and $7 for a small pizza. the number of large pizzas was two less than four times the number of medium pizzas. thenumber of small pizzas was three more than three times the number of medium pizzas. how many of each size of pizza were ordered?
Answers: 1

Mathematics, 21.06.2019 18:00
Which ordered pair is a solution to the system of linear equations? 2x + 3y= 6 –3x + 5y = 10
Answers: 1


Mathematics, 21.06.2019 18:30
Iam a rectangle. my perimeter is 60 feet. how much are do i cover?
Answers: 1
You know the right answer?
An article in information security technical report ["malicious software—past, present and future" (...
Questions


Mathematics, 04.11.2020 22:10

Mathematics, 04.11.2020 22:10

Mathematics, 04.11.2020 22:10


Chemistry, 04.11.2020 22:10



Physics, 04.11.2020 22:10

Mathematics, 04.11.2020 22:10

History, 04.11.2020 22:10


Biology, 04.11.2020 22:10

English, 04.11.2020 22:10



Mathematics, 04.11.2020 22:10

Mathematics, 04.11.2020 22:10

English, 04.11.2020 22:10

Mathematics, 04.11.2020 22:10


![E[Y]=20\times0.463=9.26](/tpl/images/0246/6567/67785.png)